DbSchema for MongoDB Databases
DbSchema is a powerful database management and design tool for MongoDB. It offers features such as visual schema design, team collaboration with GIT, schema deployment and HTML schema documentation.
How to Connect to MongoDB Database
- Access the Connection Dialog
Choose "Connect to the database" or "New Model Connected to the Database" will let you select your database and open the Connection Dialog.
DbSchema automatically downloads the JDBC driver to connect to your database.
- Configure the Connection
- Troubleshoot Firewall Issues If you encounter connection issues, it may be due to firewall settings. Read how to enable Firewall Connections.
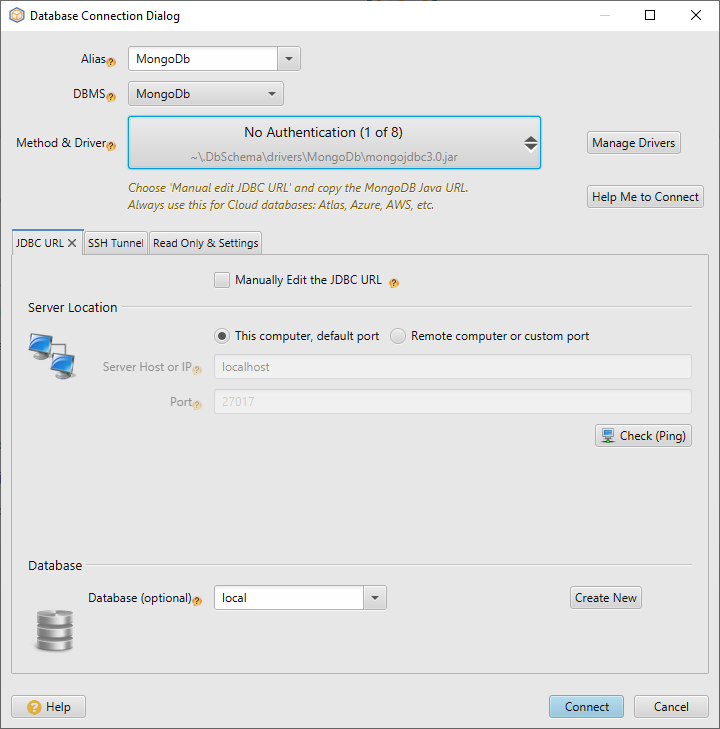
In the Connection Dialog window, select the JDBC URL you want to connect with. If your database is running in the cloud, choose Edit Manually and insert the JDBC URL from the cloud console.
Enter the host name, the authentication details, select your database as described in the Connection Dialog page.
 Firewalls & anti-viruses may block database connections.
Firewalls & anti-viruses may block database connections.
DbSchema can connect to MongoDb using the native MongoDb Java URI, by choosing 'Manually Edit JDBC URL'. Without this option you can entering the host, port, etc. and DbSchema will compose the JDBC URL.
- Connect Using MongoDb Java URI
- Connect to MongoDb Atlas Cloud
- Connect Using the Dialog Fields
- SSL/TSL & Further Connection Parameters
- How to setup authentication in MongoDb server
Connect Using MongoDb Native URI
You can connect using the Java URI as in MongoDb documentation.
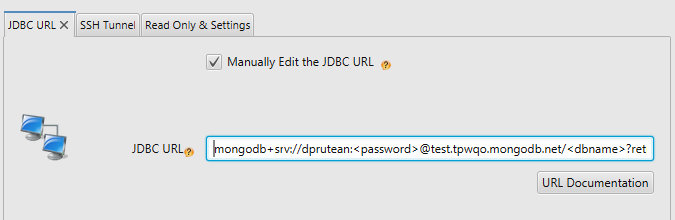
In the DbSchema Connection Dialog choose 'Manual Edit JDBC URL'.
You may connect to multiple hosts and use custom parameters.
The connection parameters are described in the MongoDB documentation.
Connect to MongoDb Atlas Cloud
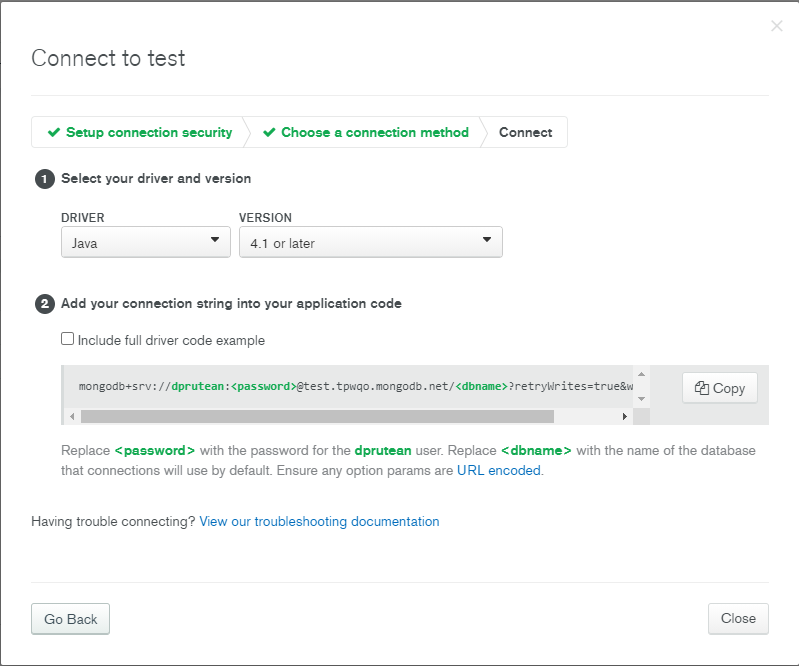
In the Atlas console choose 'Connect Cluster' to find the Java URI connection string.
There choose 'Connect using Application' and 'Java' latest version.
Copy the URL in the DbSchema 'Manual Configure JDBC URL' filed.
This is the same procedure as in the chapter above.
Connect Using the Dialog Fields
In the connection dialog you can enter the host, port, user and password ( by default not required ). From the Driver combo you can choose between connecting without authentication and with authentication.
The connection without authentication is the default one, unless you or an admin have set authentication on the server.
SSL/TSL & Further Connection Parameters
To add additional connectivity parameters and SSL/TLS, please press 'Manually Edit JDBC URL' and add parameters like in the MongoDB Java Driver Documentation. Use '&' as separator. The main parameters you can use:
- Use DNS seed list connection string with mongodb+srv Example: mongodb+srv://server.example.com/
- ssl=true/false - to enable disable TLS/SSL
- tlsCertificateKeyFile Specifies the location of a local .pem file that contains either the client's TLS/SSL X.509 certificate or the client's TLS/SSL certificate and key
- tlsCertificateKeyFilePassword Specifies the password to de-crypt the tlsCertificateKeyFile.
- tlsCAFile Specifies the location of a local .pem file that contains the root certificate chain from the Certificate Authority. This file is used to validate the certificate presented by the mongod/mongos instance.
- tlsAllowInvalidCertificates Bypasses validation of the certificates presented by the mongod/mongos instance
- tlsAllowInvalidHostnames Disables hostname validation of the certificate presented by the mongod/mongos instance.
- tlsInsecure Disables various certificate validations.
JVM System Properties for TLS/SSL
TLS/SSL can be enabled by editing the file DbSchema.vmoptions located in the same folder as DbSchema executable or ./DbSchema.app/Contents/vmoptions.txt on Mac OS, and adding one of the parameters below. A typical application will need to set several JVM system properties to ensure that the client is able to validate the TLS/SSL certificate presented by the server:- javax.net.ssl.trustStore: The path to a trust store containing the certificate of the signing authority
- javax.net.ssl.trustStorePassword: The password to access this trust store
|
- javax.net.ssl.keyStore The path to a key store containing the client’s TLS/SSL certificates
- javax.net.ssl.keyStorePassword The password to access this key store
The connection without authentication is the default one, unless you or an admin have set authentication on the server.
How to setup authentication in MongoDb server
To setup authentication in MongoDb follow this steps:-
Create the user in database:
use admin db.createUser( { user: "test", pwd: "test", roles: [ { role: "root", db: "admin" } ] } ); -
Create a file mongo.config in the MongoDB installation folder. Edit to
# Basic database configuration dbpath = C:\data\db bind_ip = 127.0.0.1 port = 27017 # Security auth = true # Administration & Monitoring nohttpinterface = true - Start the mongodemon using mongod.exe -f mongo.config. You can text the connection using mongo.exe --port 20571 -u test -p test --host 127.0.0.1 admin .